NCSAM was created in 2003 by the U.S. Department of Homeland Security and National Cyber Security Alliance to ensure everyone has the resources they need to stay safe and secure online. The goal of NCSAM is to increase the awareness of the ever-evolving cybersecurity landscape and bring attention to different steps people can take to protect their information.
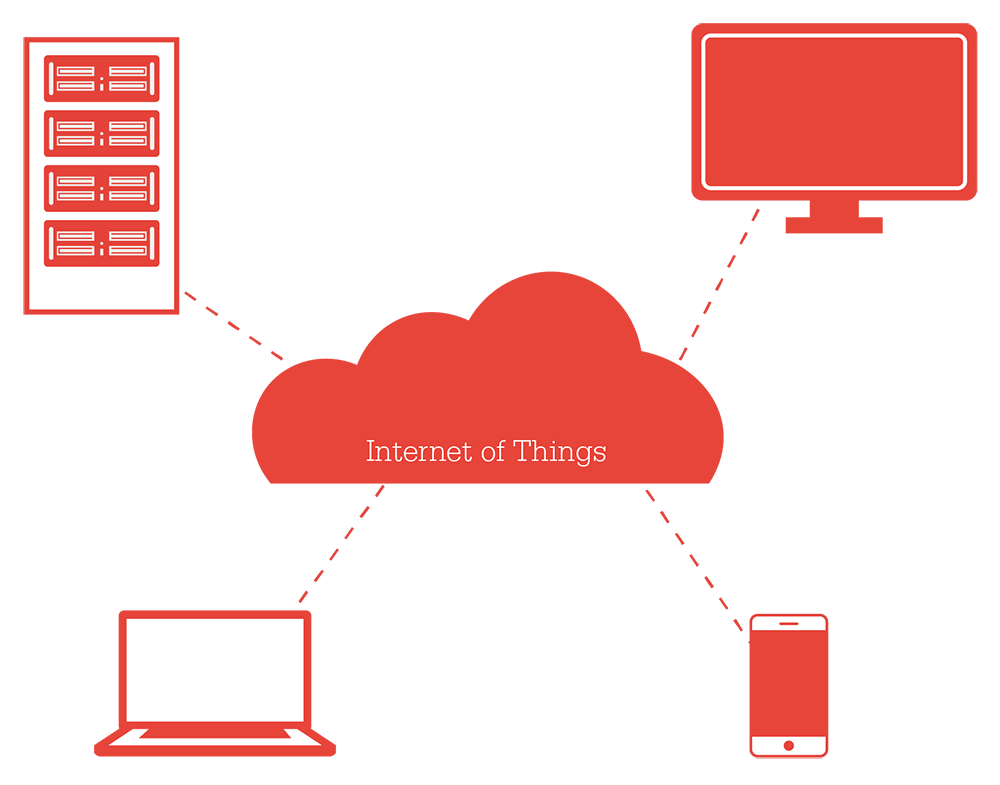
Continue reading →By 2020 – a mere three years from now – research has projected there will be more than 20 billion connected devices on the planet. That’s an average of roughly four per person, ranging from tablets to eyeglasses and houses to cars. The Internet of Things is expected to transform everyday life as we know it in areas ranging from home comfort to health care.
Continue reading →As our collective and individual digital worlds continue to expand, we create and rely on more and more personal data being in the digital realm. In the process, our personal data becomes worth as much as – or more than – any valuable possession (family jewels, anyone?) we might lock up and safely store. That data also is every bit as vulnerable, maybe even more so.
Continue reading →We spend a lot of money to secure our information. In fact, cybersecurity is one of the globe’s fastest-growing industries. According to Gartner, IT security spending will top $81.6 billion for 2016, an increase of 7.9 percent over 2015, and that market is expected to more than double in just three years.
Continue reading →We just finished up exhibiting at the Enfuse conference, where we had a chance to catch up with investigators and IT people from various government agencies, as well as private sector companies. We had fun sharing the news about our new Ditto DX imager and how it will speed up data acquisition, especially for those who have incorporated Logical Imaging into their workflows. And we continue to be pleasantly surprised by those who see the value of forensic acquisition in e-discovery. In fact, one of our name-brand customers in the world of cyber security has created a workflow for their seven global regions to create an archive of ex-employee data for future investigation or litigation.
Continue reading →Did you know that we provide data transport and storage solutions for many different industries? Check out our industry pages to find out more about how CRU can provide your business with high-quality products to fit your particular requirements. (And if you have any special requests, let us know!)
Continue reading →We are so excited to announce the opening of the 2015 Photography Contest! It is one of our favorite times of the year. Amateur and professional photographers are invited to submit their photographs from now until September 15, 2015, at www.cru-inc.com/photocontest. Prizes include storage backup devices—same ones the pros use to protect their life’s work.
Continue reading →This post is a part of a six-part series from the white paper "The Measure of an Enclosure-Five Factors to Consider When Choosing External Data Storage". Can't wait to read the whole paper? You don't have to! Read it right here. The paper includes a glossary, charts and illustrations to help explain further.
Continue reading →Did you know that 53% of small- and medium-sized businesses have experienced data loss within the last 12 months?
Continue reading →The CRU® Mouse Jiggler MJ-3 has many fun uses; and PC gamers, IT professionals, and presenters keep the Mouse Jiggler MJ-3 close at hand for many reasons.
What makes this compact device so cool?